How To Start A Cyber Security Company From Scratch 2024

The digital landscape continues to expand rapidly, with billions of individuals worldwide engaging in mobile technology. However, alongside this growth comes an alarming rise in security threats, making data protection more critical than ever.
This escalating need for cybersecurity presents a vast market opportunity. While competition in the field is fierce, the market remains far from saturated, offering ample room for new entrants. If you’re considering launching a cybersecurity company, now could be an opportune moment. In this article, we provide guidance and assistance to help you navigate the process effectively.
According to PayScale data, businesses are willing to pay $150 per hour or more for experienced cybersecurity consultants who can fortify their systems and networks against cybercrime.
So if you’re ready to enter into one of the fastest-growing industries with high demand for skilled professionals, keep reading! We’ve got you covered on everything you need to know about how to start a cyber security company.
What is Cyber Security Business?
A cyber security business is a company that specializes in providing products and services aimed at protecting individuals, organizations, and systems from cyber threats and attacks. These businesses offer a wide range of solutions, including security software, hardware, consulting services, risk assessments, incident response, and training.
Their primary goal is to safeguard digital assets, sensitive information, networks, and infrastructure against unauthorized access, data breaches, malware, ransomware, phishing, and other cyber risks. Cyber security businesses play a crucial role in helping clients mitigate risks, comply with regulations, and maintain a secure and resilient digital environment.
How to Start a Cyber Security Company/Business?

Here are the key steps to start a cyber security company:
1) Obtain the Appropriate Professional Certifications
When establishing credibility in the cybersecurity or IT industry, having the right certifications is essential. While a bachelor’s degree in fields like information technology or computer science is advantageous, certifications demonstrate practical skills and expertise that clients value.
- Certified Ethical Hacker Certification: Offered by the EC-Council, this certification is for cybersecurity professionals who assess networks and systems for vulnerabilities. The exam, priced at $100, comprises 125 questions and lasts approximately four hours.
- GIAC Security Essentials Certification (GSEC): Provided by Global Information Assurance Certification (GIAC), this certification validates the information security knowledge of IT professionals. The exam, costing $150, covers 180 questions and takes about five hours to complete.
- Certified Information Systems Security Professional (CISSP): Issued by (ISC)², CISSP demonstrates the ability to design, implement, and maintain effective cybersecurity programs and systems. The exam, priced at $699, consists of a maximum of 150 questions and lasts three hours.
- Certified Cloud Security Professional (CCSP): Also from (ISC)², CCSP showcases proficiency in designing, maintaining, and securing cloud data, applications, and infrastructure. The exam, priced at $599, contains 125 questions and takes four hours to complete.
- CompTIA Cybersecurity Analyst (CompTIA CySA+): Evaluating threat detection skills and the ability to analyze data, CompTIA CySA+ costs $359, includes up to 85 questions, and lasts under three hours.
- ISACA’s Certified in the Governance of Enterprise IT (CGEIT): This certification demonstrates the ability to audit, control, and secure information systems. Non-members pay $760, while members pay $575 for the exam, which lasts four hours and contains 150 questions.
- ISACA’s Certified Information Security Manager (CISM): Also from ISACA, CISM indicates expertise in managing information systems and IT security. The exam, priced at $760 for nonmembers and $575 for members, consists of 150 questions and lasts four hours.
While certifications are crucial, they’re just one aspect of starting a successful cybersecurity business. Creating a robust business plan and executing it effectively are equally important steps in building a thriving venture.
2) Craft a Tailored Business Plan for Cybersecurity
A well-structured business plan serves as the cornerstone of your cybersecurity venture, offering a roadmap for success. Here are the essential elements to include, as recommended by the U.S. Small Business Administration (SBA):
- Executive Summary: Provide a concise overview of your cybersecurity business, highlighting its unique value proposition and key factors contributing to its success.
- Company Description: Offer a comprehensive overview of your company, including its mission, vision, goals, and core values.
- Market Analysis: Conduct a thorough competitive analysis to identify your target market and assess the competitive landscape. Determine whether your competitors are specialized cybersecurity consultants or providers offering general IT services.
- Legal Structure: Define the legal structure of your business, whether it’s a sole proprietorship, partnership, limited liability company (LLC), or corporation.
- Products or Services: Clearly outline the cybersecurity products or services you plan to offer, emphasizing their unique features and benefits.
- Marketing and Sales Strategy: Develop a robust marketing and sales strategy to attract clients and generate revenue. Consider leveraging digital marketing tactics, networking events, and partnerships within the cybersecurity industry.
- Funding/Budget Plan: Determine your funding requirements and create a detailed budget plan to manage expenses effectively. Explore various funding options, such as loans, investments, or bootstrapping.
- Financial Projections: Provide realistic financial projections indicating when your cybersecurity business is expected to achieve profitability. Include revenue forecasts, expense estimates, and cash flow projections.
By meticulously addressing these components in your business plan, you’ll lay a solid foundation for your cybersecurity venture and increase your chances of long-term success.
3) Identify and Analyze Your Target Market
In the early stages of establishing your cybersecurity business, defining your target market is paramount. Consider the following strategies to refine your focus:
- Industry Specialization: Determine if you want to cater to a specific industry, such as finance or healthcare, and position your business as an authority in that sector.
- Cybersecurity Niche: Explore opportunities to specialize in a particular area of cybersecurity, such as access control or network security, irrespective of industry.
- Market Analysis: Conduct thorough research to understand your competitors and identify potential opportunities in the cybersecurity landscape. Ask critical questions like:
- Who are your current competitors?
- What are their strengths and weaknesses?
- How does your business differentiate itself from competitors?
- What strategies can you employ to capture market share from competitors?
- How might competitors react to your market entry?
- SWOT Analysis: Utilize the SWOT (Strengths, Weaknesses, Opportunities, Threats) framework to assess your business’s positioning in the market. This exercise helps identify internal strengths and weaknesses, as well as external opportunities and threats.
3) Choosing a Legal Structure
Once you’ve defined your market focus and assessed the competitive landscape, determine the most suitable legal structure for your cybersecurity business. Consider options such as sole proprietorship, partnership, limited liability company (LLC), or corporation.
By carefully defining your target market, analyzing the competition, and selecting an appropriate legal structure, you can establish a solid foundation for your cybersecurity venture.
4) Selecting the Legal Structure for Your Company
Determining the legal structure of your cybersecurity business is a pivotal decision that influences various aspects of your operations, taxation, and financial liabilities. Consider the following common company structures outlined by the Small Business Administration (SBA) to guide your decision-making process:
- Sole Proprietorship: This straightforward structure involves a single individual owning and operating the business. While easy to establish, sole proprietorships expose the owner to personal liability for business debts and obligations, as there is no legal separation between the individual and the business entity.
- Partnership: Partnerships are formed by two or more individuals who share ownership and management responsibilities. Partners report profits and losses on their personal tax returns. Limited partnerships (LPs) and limited liability partnerships (LLPs) offer varying degrees of liability protection and control for partners.
- Limited Liability Company (LLC): LLCs combine elements of both sole proprietorships and partnerships, providing owners with limited liability protection while allowing them to report business income on their personal tax returns. This structure offers a degree of asset protection by separating personal and business assets.
- S Corporation: S corps offer tax advantages by allowing owners to receive profits as distributions, subject to lower tax rates. However, owners must pay themselves a reasonable salary and are responsible for payroll taxes. Compliance with additional regulations and paperwork is required for this structure.
- C Corporation: C corps are separate legal entities that can generate profits, incur taxes, and assume legal liabilities independently from their shareholders. While shareholders benefit from limited liability, they may face double taxation on corporate earnings and dividends.
Before finalizing your business structure, seek guidance from business advisors, accountants, and legal professionals to evaluate the implications of each option and determine the most suitable arrangement for your cybersecurity venture.
5) Acquire Necessary Business Documentation and Financial Tools
Securing essential documentation and financial tools is crucial for the smooth operation of your cybersecurity business. Here’s what you need to consider:
- Business License and Permits: Consult with state and local authorities to determine the specific business licenses or permits required to establish your cybersecurity venture. While federal licensing may not be mandatory at this stage, compliance with state and local regulations is essential. Additionally, certain jurisdictions may mandate the procurement of general liability insurance before issuing a license. If you intend to hire employees, ensure compliance with workers’ compensation insurance requirements.
- Business Bank Account: Opening a dedicated business bank account is imperative to segregate your personal and business finances effectively. While it may be convenient to opt for your personal bank, explore alternatives such as online, national, or local banks offering fee-free business accounts tailored to your needs.
- Company Credit Card: Consider obtaining a business credit card to streamline financial transactions and facilitate expense management. A business credit card offers several advantages, including improved financial visibility, enhanced purchasing power, and potential rewards or cashback benefits. Evaluate different card options based on your business requirements and eligibility criteria, keeping in mind that your personal credit score may influence available offers.
By obtaining the necessary licenses, establishing a dedicated business bank account, and acquiring a company credit card, you can lay a solid foundation for the financial management and regulatory compliance of your cybersecurity enterprise.
6) Secure Financing and Establish Financial Guidelines
Securing adequate funding is essential for launching your cybersecurity venture. Explore various funding avenues, including personal capital, loans, grants, and angel investors, to kickstart your business endeavors.
Notably, the cybersecurity sector has garnered significant attention from venture capitalists, with recent reports indicating substantial investments totaling billions of dollars.
Consider reaching out to reputable investors specializing in cybersecurity ventures, such as Strategic Cyber Ventures, ForgePoint Capital, or Intel Capital, to explore potential funding opportunities.
Setting and adhering to a well-defined budget is crucial for the financial stability and sustainability of your cybersecurity startup. Here are some key budgeting principles to consider, as recommended by The Balance:
Establish clear sales revenue goals to guide your financial projections and business growth strategies.
- Thoroughly understand your operating expenses, including overhead costs, employee salaries, and technology investments.
- Maintain diligent cash flow management to ensure sufficient liquidity for day-to-day operations and future growth initiatives.
- Allocate funds for an emergency fund to mitigate unforeseen financial challenges or market fluctuations effectively.
7) Selecting an Optimal Business Location
Choosing the right location for your cybersecurity business involves careful consideration of various factors, including accessibility, cost-effectiveness, and business growth opportunities. Here are some location options to contemplate:
- Home-based operation: Operating your business from home offers flexibility and cost savings, eliminating the need for a separate office space. However, it requires self-discipline and may lack the collaborative environment of traditional workplaces.
- Co-working spaces: Co-working spaces provide a conducive work environment with shared amenities and networking opportunities. While offering flexibility, they may impose limitations on privacy and scalability.
- Leasing or purchasing office space: Establishing a dedicated commercial office space provides tax benefits and a professional setting for client meetings. However, upfront costs and long-term commitments should be carefully evaluated.
Regardless of your chosen location, ensure compliance with insurance requirements. Commercial property insurance is essential for leased or owned office spaces, safeguarding your business assets against unforeseen events. Additionally, consider commercial auto insurance if your business involves on-site client visits, providing comprehensive coverage for business-related vehicle usage.
8) Promote Your Services Effectively
Customers are the lifeblood of your cybersecurity business, making marketing a crucial aspect of your success. If you’re not adept at marketing, consider hiring professionals to help you launch your brand and services effectively.
Start by establishing a strong online presence with a well-designed website, optimized for search engines and user engagement. Your website serves as your primary marketing asset, so invest time and effort into its development to attract potential clients.
Utilize social media platforms like LinkedIn, Facebook, and Twitter to engage with your target audience and share valuable cybersecurity insights. If feasible, enlist the services of a content consultant to maintain an active blog and enhance your online visibility. Additionally, explore offline marketing opportunities by attending cybersecurity conferences and networking events to forge valuable connections within the industry.
9) Craft Comprehensive Client Contracts
Before embarking on any project, ensure you have robust client service agreements in place to protect both parties involved. These contracts should clearly outline project scope, intellectual property ownership, payment terms, and liabilities to mitigate potential disputes.
Consider seeking legal assistance to draft or review client contracts to safeguard your business interests effectively. Investing in cyber liability insurance and technology errors and omissions (E&O) insurance can provide additional protection against unforeseen risks and liabilities.
10) Recruit Top Talent
As your business grows, hiring quality employees becomes essential to sustain your success. Conduct thorough interviews and background checks to vet potential candidates and ensure they possess the necessary skills and experience.
Comply with federal and state laws throughout the hiring process, and secure workers’ compensation insurance to safeguard both your employees and your business. Additionally, consider purchasing fidelity bonds to protect against employee-related risks such as theft or fraud.
11) Protect Your Business Investment
Launching a new cybersecurity venture is an investment in your future, requiring diligent risk management and protection strategies. Explore insurance options tailored to cybersecurity businesses to mitigate potential financial losses and liabilities.
Cybersecurity Business Plan

This detailed business plan outlines the strategic framework for establishing and operating a successful cybersecurity business, poised to address the evolving challenges of cyberspace and meet the growing demand for cybersecurity services.
The cybersecurity business will operate as a specialized consultancy firm, catering to businesses, government agencies, and non-profit organizations. Core services include:
- Cyber Threat Assessment and Analysis: Conducting thorough assessments to identify and analyze potential cyber threats and vulnerabilities within clients’ systems and networks.
- Incident Response and Recovery: Providing rapid response and recovery services to mitigate the impact of cybersecurity incidents, such as data breaches and malware attacks.
- Risk Management and Compliance: Assisting clients in implementing robust risk management frameworks and ensuring compliance with industry regulations and cybersecurity standards.
- Security Awareness Training: Developing customized training programs to educate employees on cybersecurity best practices and raise awareness about emerging threats.
1) Market Analysis:
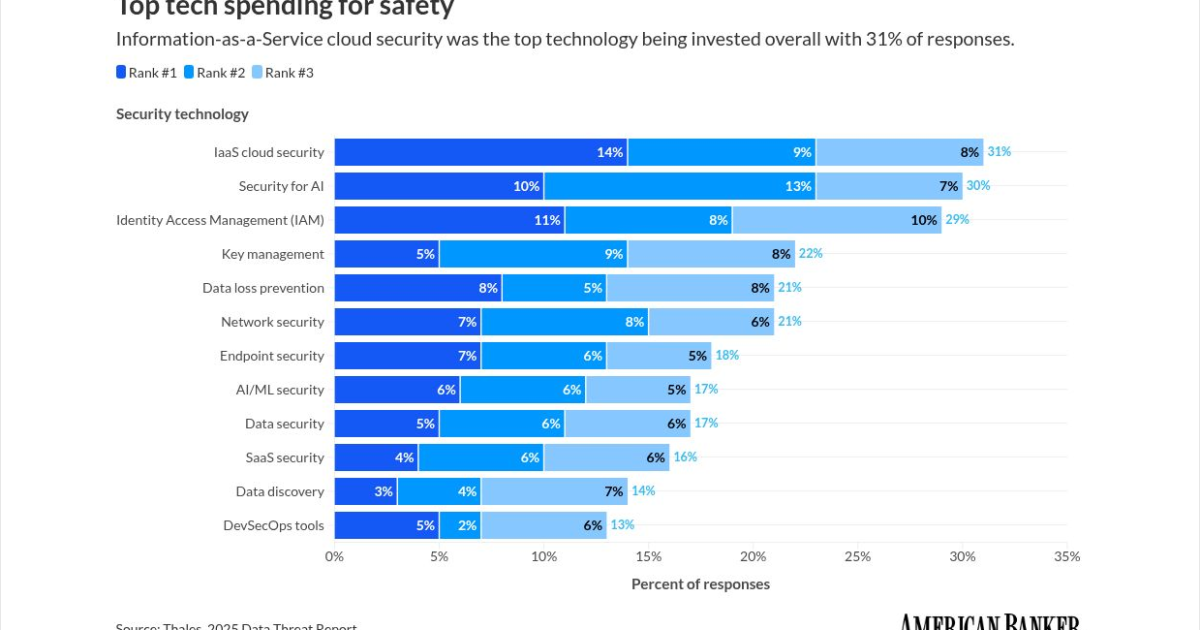
The cybersecurity market is experiencing significant growth due to the increasing frequency and complexity of cyber attacks. Businesses across all sectors are investing heavily in cybersecurity solutions to protect their digital assets, driving the demand for specialized cybersecurity services.
With cybersecurity becoming a top priority for organizations worldwide, the market for cybersecurity services is expected to continue expanding in the coming years.
2) Target Market:
The target market includes small and medium-sized enterprises (SMEs), large corporations, government agencies, and non-profit organizations seeking reliable cybersecurity solutions. Initially focusing on local businesses within the region, the business aims to gradually expand its reach to national and international markets.
3) Marketing and Sales Strategy:
To reach the target audience effectively, the business will employ a multi-channel marketing approach, including digital marketing, social media outreach, industry partnerships, and participation in cybersecurity events and conferences. Additionally, leveraging professional networks and client referrals will generate leads and expand the customer base.
4) Operational Plan:
The cybersecurity business will operate from a centralized office equipped with state-of-the-art technology infrastructure and cybersecurity tools. A team of cybersecurity experts will work collaboratively to deliver high-quality services, adhering to industry best practices and ethical standards. Ongoing training and professional development will ensure the team remains at the forefront of cybersecurity innovation.
5) Financial Projections:
Based on thorough market research and projected growth trends, steady revenue growth is anticipated in the initial years of operation, with profitability expected to be achieved by the end of the second year. Detailed forecasts for revenue, expenses, cash flow, and profitability are included, supported by conservative assumptions and risk mitigation strategies.
Is Cyber Security Business Profitable?
Yes, a cybersecurity business can be highly profitable given the increasing demand for cybersecurity services in today’s digital landscape. Here are several factors contributing to the profitability of cybersecurity ventures:
- Growing Demand: With the rise in cyber threats and cybercrime incidents, businesses of all sizes are prioritizing cybersecurity to protect their sensitive data and digital assets. This growing demand for cybersecurity solutions creates ample opportunities for businesses offering specialized services.
- Regulatory Compliance: Many industries are subject to stringent data protection regulations and compliance requirements, such as GDPR, HIPAA, and PCI DSS. Organizations must invest in cybersecurity solutions to ensure compliance with these regulations, driving the demand for cybersecurity services.
- Evolving Threat Landscape: Cyber threats are becoming increasingly sophisticated and diverse, posing significant challenges to businesses worldwide. As cyber attackers continuously adapt their tactics, businesses rely on cybersecurity experts to implement proactive measures and mitigate emerging threats effectively.
- Business Continuity: Cybersecurity breaches can have devastating consequences for businesses, including financial losses, reputational damage, and operational disruptions. Investing in cybersecurity measures is essential for maintaining business continuity and safeguarding long-term profitability.
- Scalability: Cybersecurity services can be scaled to accommodate the needs of clients ranging from small businesses to large enterprises. As a cybersecurity business grows its client base and expands its service offerings, it can achieve scalability and increase its revenue potential.
How to Get Clients for Cyber Security Companies?
Getting clients for a cybersecurity company involves strategic marketing, networking, and demonstrating expertise in the field. Here are some effective strategies to attract clients to your cybersecurity business:
1) Develop a Strong Online Presence:
Create a professional website that highlights your services, expertise, and success stories. Optimize your website for search engines to improve visibility and attract organic traffic. Use content marketing tactics such as blogging, whitepapers, and case studies to showcase your knowledge and establish credibility in the industry.
2) Leverage Social Media:
Utilize social media platforms such as LinkedIn, Twitter, and Facebook to engage with potential clients and industry professionals. Share valuable insights, cybersecurity tips, and industry news to position yourself as a thought leader. Join relevant groups and participate in discussions to expand your network and reach.
3) Offer Thought Leadership:
Publish articles, research papers, and presentations on cybersecurity topics to demonstrate your expertise. Speak at industry events, conferences, and webinars to showcase your knowledge and build credibility. Contributing to reputable publications and participating in panel discussions can also enhance your visibility and attract potential clients.
4) Network with Industry Professionals:
Attend cybersecurity conferences, trade shows, and networking events to connect with industry professionals, potential clients, and strategic partners.
Building relationships with key stakeholders in the cybersecurity ecosystem can lead to referrals and business opportunities. Join professional associations and online communities to expand your network and stay updated on industry trends.
5) Provide Exceptional Service:
Deliver high-quality cybersecurity services that exceed client expectations. Satisfied clients are more likely to refer your business to others and provide positive testimonials and reviews. Focus on building long-term relationships with clients by offering personalized solutions, proactive support, and ongoing cybersecurity education.
6) Offer Free Assessments or Consultations:
Provide complimentary cybersecurity assessments or consultations to prospective clients to demonstrate the value of your services and identify their specific needs and challenges. Use these opportunities to showcase your expertise, propose tailored solutions, and establish trust with potential clients.
7) Partner with Complementary Businesses:
Collaborate with other businesses that offer complementary services, such as IT consulting firms, software vendors, or managed service providers. Establishing strategic partnerships can help you access new client bases, leverage existing relationships, and offer comprehensive cybersecurity solutions to mutual clients.
By implementing these strategies consistently and effectively, you can attract clients to your cybersecurity company and position yourself as a trusted advisor in the industry. Building a strong reputation, fostering relationships, and delivering exceptional service are key to long-term success in the competitive cybersecurity market.
Summing Up!
Starting a cyber security company may seem daunting, but it is not an impossible feat. With the right knowledge, resources, and determination, anyone can turn their passion for protecting others into a successful business venture.
Throughout this blog post, we have discussed the key steps of how to start a cybersecurity company, from understanding the market and identifying your target audience to building a strong team and establishing partnerships.
So go ahead and take that first step towards starting your own cyber security company today! Your contribution to the ever-evolving field of technology could make all the difference in safeguarding against cyber threats.
Key Highlights
- The digital era has spurred a surge in cybersecurity threats, creating a high demand for effective security solutions.
- With cyber-attacks projected to cause trillions of dollars in damages annually by 2025, the cybersecurity market offers significant profit potential.
- The evolving nature of cyber threats presents opportunities for innovative solutions and services within the cybersecurity industry.
- Despite intense competition, the cybersecurity market is far from saturated, making it an ideal time to enter the industry and establish a successful cybersecurity company.
FAQ’s
What qualifications or certifications do I need to start a cybersecurity company?
Answer: While formal education in fields such as information technology or computer science is beneficial, obtaining relevant certifications is crucial. Certifications like Certified Ethical Hacker (CEH), Certified Information Systems Security Professional (CISSP), and CompTIA Security+ demonstrate your expertise and credibility in the cybersecurity domain.
How much funding is required to start a cybersecurity business?
Answer: The amount of funding needed varies based on factors like business size, location, and services offered. Expenses may include certifications, equipment, marketing, and operational costs. It’s advisable to create a detailed business plan to estimate startup expenses accurately.
What legal structure should I choose for my cybersecurity company?
Answer: Common legal structures for businesses include sole proprietorship, partnership, limited liability company (LLC), S corporation, and C corporation. Each structure has its own advantages and implications in terms of taxation, liability, and management.
How can I attract clients to my cybersecurity company?
Answer: Building a strong online presence through a professional website, social media, and content marketing is essential. Networking at industry events, joining cybersecurity communities, and offering valuable insights through blogs or webinars can also help attract clients.
What services should I offer as a cybersecurity company?
Answer: Depending on your expertise and target market, services may include risk assessment, penetration testing, security audits, incident response, threat intelligence, and security awareness training. Tailor your services to address the specific needs and challenges of your clients.
Related
link